Technology Blog
From token generation events and drone regulation to the latest developments in privacy and data security compliance, our Technology Industry Blog focuses on the still-evolving regulatory landscape for companies developing new products and services, as well as those for whom technology figures prominently into their day-to-day operations.
Many of our contributors are IAAP-certified privacy professionals or hold advanced STEM degrees, with prior experience working as systems engineers and software developers. As a result, our blog offers that rare coupling of legal insight and technical sophistication, making it a true resource for businesses operating at the bleeding edge, where reliable legal intel can prevent project delays as well as civil and criminal exposure.
Recent Blog Posts

July 15, 2024 | Publications
Businesses developing or using artificial intelligence (AI) systems in Colorado may be required to a...

July 10, 2024 | Publications
This is the fifth in a series of articles outlining how businesses can successfully capitalize on th...

June 18, 2024 | Publications
The U.S. Court of Appeals for the Federal Circuit shook things up on May 23, 2024, with an en banc p...

May 1, 2024 | Publications
*This article was published by Security Info Watch on May 17, 2024. The American Privacy Rights Act ...

April 18, 2024 | Publications
The Kentucky Consumer Data Protection Act, or KCDPA, was signed into law by Governor Andy Beshear on...

April 15, 2024 | Publications
Artificial intelligence (AI), particularly in the form of large language models (LLMs), has become a...

April 9, 2024 | Publications
*This article was also published in Pratt’s Energy Law Report’s June 2024 edition. This ...

March 12, 2024 | Blogs
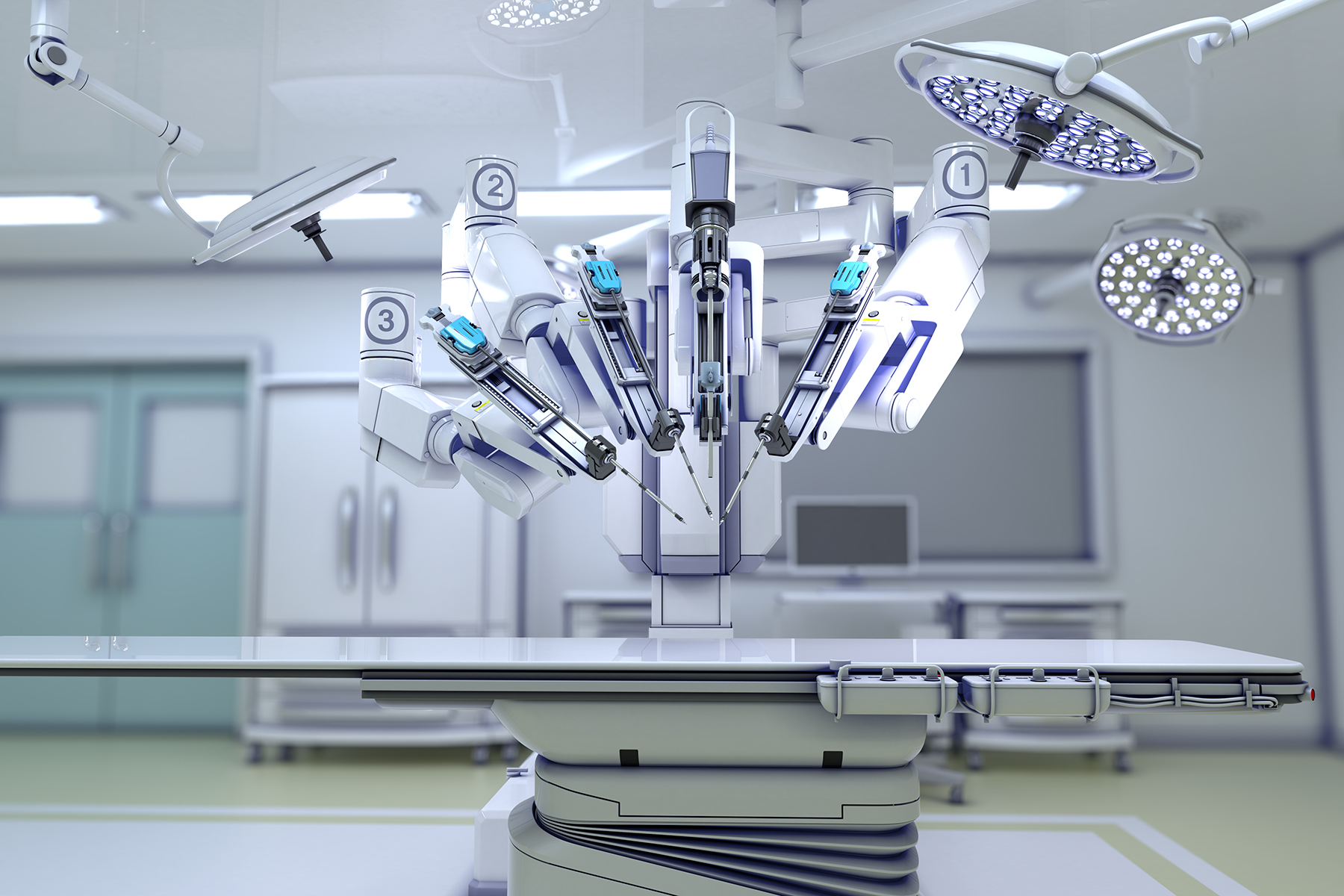
Artificial intelligence (AI) applications in health care can create better, stronger, and faster sol...

February 16, 2024 | Publications
This is the second in a series of articles outlining successful approaches to integrating AI into bu...

February 14, 2024 | Publications
In the 1990s, as today, the internet ran on content, which meant that it both had, and was, a proble...

February 4, 2024 | Publications
How to perfectly surf the artificial intelligence (AI) wave is a challenge for many businesses and t...

January 8, 2024 | Blogs
Recent Kentucky tax legislation continued to expand the landscape of services subject to sales and u...

December 26, 2023 | Blogs
This was originally published in Reuters Legal News (December 14, 2023). Attempts to protect AI gen...

November 14, 2023 | Publications
President Biden’s executive order (EO) on artificial intelligence (AI) is a call to action for the...
November 9, 2023 | Blogs
*This article was originally published in Law360 Expert Analysis. Artificial intelligence models a...

November 1, 2023 | Blogs
As news comes out every week about new technologies, from new crypto wallets to generative AI to sel...

October 2, 2023 | Blogs
Artificial Intelligence (AI) is one of those high-risk, high-reward opportunities that is irresistib...

September 15, 2023 | Blogs
Businesses that collect or process health data from individuals are subject to new and burdensome re...

August 29, 2023 | Publications
*This article was originally published by Marine Log. Pick your industry and you will quickly conc...

August 29, 2023 | Blogs
This article explores recent developments in the U.S. federal taxation of virtual currencies by the ...

August 2, 2023 | Blogs
This article was originally published in Indiana Lawyer. Advances in artificial intelligence (AI) ...

July 25, 2023 | Blogs
Most virtual asset providers are aware of federal-level guidance, such as the money services busines...

July 25, 2023 | Publications
The Federal Trade Commission (FTC) recently updated its Guides Concerning the Use of Endorsements an...

June 26, 2023 | Publications
Business email compromise (BEC) fraud is the number one cybercrime faced by American businesses, as ...

June 2, 2023 | Publications
On May 29, 2023, the Texas legislature passed the Texas Data Privacy and Security Act (TDPSA). The b...

May 26, 2023 | Blogs
Business leaders will find important information in the #StopRansomware Guide developed through the ...

April 27, 2023 | Blogs
On April 11, Indiana’s state legislature passed a comprehensive state privacy legislation Senate B...

April 20, 2023 | Publications
Three Canadian primary eastern seaports suffered a cyberattack, once again raising issues of data se...

March 29, 2023 | Publications
…And you’re probably right. On March 2, the Biden administration issued its long-awaited Nationa...

March 24, 2023 | Publications
On March 15, the Iowa state legislature passed a comprehensive state privacy legislation (“SF 262�...

March 16, 2023 | Failed-Bank Response Team
Bank customers currently overwhelmed by mitigating risks associated with accounts, fund recovery and...

March 13, 2023 | Blogs
On November 28, 2022, the United States Department of Treasury’s Office of Foreign Assets Cont...

February 22, 2023 | Publications
Governments and private companies are engaged in a modern gold rush to the stars. After a number of ...

January 26, 2023 | Blogs
Tech giants like Google, Apple, and Facebook incur huge Euro fines from European Union data privacy ...

January 13, 2023 | Blogs
A third way emerges – light touch India -soon to be the world’s most populous country, a fast gr...

January 11, 2023 | Blogs
Identity management. Learn how an automated approach can defend against the rising tide of data hack...

January 6, 2023 | Publications
With the arrival of 2023, we have some thoughts on the ever-growing cyber threats to our digital inf...

January 4, 2023 | Publications
In 1996, the Communications Decency Act was passed to provide incentives and protections for “inte...

January 3, 2023 | Blogs
November 2022 Data Privacy News November 2022 saw the largest private data privacy settlement in U.S...

December 6, 2022 | Blogs
A systemic approach to minimizing data theft and maximizing data security Decentralized identifiers ...

November 29, 2022 | Blogs
How over-focus on data breach fails to achieve data privacy and security Breached!, published in 202...

November 23, 2022 | Blogs
October 2022 highlights for data privacy: Battle between the U.S. Federal Trade Commission and a dat...

November 10, 2022 | Blogs
How AI and Big Data are Changing the World William McKnight, one of the most highly published analys...

November 7, 2022 | Blogs
The FTC Sues a Broker for Unfair Business Practices, and the Broker Responds Data brokers acquire an...

October 31, 2022 | Blogs
On September 30, 2022, the United States Department of Treasury’s Office of Foreign Assets Control...

October 28, 2022 | Blogs
The Impact on Consumers and Company Personnel Data breaches are now daily news, like weather reports...

October 17, 2022 | Blogs
Addressing a Threat to Personal Data Privacy Spell-jacking – a new word emerging from the tech...

October 13, 2022 | Blogs
The Department of Homeland Security (DHS) first declared October “Cybersecurity Awareness Month”...

October 6, 2022 | Blogs
October is Cybersecurity Awareness Month Cybersecurity Awareness Month is co-led by the National Cyb...

October 4, 2022 | Blogs
How a California statute works in practice. In August 2022, California’s Attorney General settled ...

September 8, 2022 | Blogs
Get an update on lawsuits launched and settled in August 2022. Consider FBI warnings about DeFi plat...

August 30, 2022 | Blogs
Is the Law Ready to Protect Our Privacy? Data privacy and the laws that protect our personal informa...

August 19, 2022 | Blogs
Data localization We’ve devoted several episodes to what countries are doing to control and restri...

August 2, 2022 | Blogs
Cryptography comes from the ancient Greek word “cryptos,” meaning “hidden” or “secret.” ...

July 29, 2022 | Blogs
The buzzword for the new generation of mobile networking. 5G brings blazing speed to digital communi...

July 19, 2022 | Podcast
TikTok built a global platform sharing short videos of wild and wonderful doings of people, animals,...

July 18, 2022 | Blogs
On June 21, the U.S. House of Representatives introduced a draft federal privacy bill named the Amer...

July 14, 2022 | Blogs
Much discussion has been had recently about the fact that cryptocurrencies (tokens and coins) do not...

July 13, 2022 | Blogs
In bankruptcy parlance, the lookback period does not look good for the crypto industry. In the last ...

July 11, 2022 | Blogs
News outlets and industry publications have been publishing information about recent “crypto winte...
July 7, 2022 | Blogs
How to Protect Sensitive Personal Healthcare Information With the reversal of Roe v. Wade by the U.S...

June 23, 2022 | Blogs
Cryptocurrency has long been the digital Wild West—the legal system has been working to catch up t...

June 14, 2022 | Blogs
Protecting and using personal information has focused on computer and software technology. With the ...

June 13, 2022 | Blogs
Following President Joe Biden’s outlining the national policy on digital assets and technologies, ...

June 10, 2022 | Blogs
What’s at stake as Congress considers a national data privacy law? The National Restaurant Associa...

June 8, 2022 | Blogs
On June 1, 2022, the Department of Justice (DOJ) announced the indictment of a former product manage...

May 23, 2022 | Blogs
Through a new cybersecurity regulation, businesses in India will have six hours to report cyberattac...

May 20, 2022 | Blogs
Are decentralized autonomous organizations (DAOs) de facto general partnerships such that their “m...

May 18, 2022 | Publications
When Connecticut passed S.B. No. 6 – Connecticut Data Privacy Act (CTDPA), it became the fifth sta...

May 17, 2022 | Blogs
Japan is a major U.S. ally commercially and otherwise. What is the Japanese approach to personal dat...

April 26, 2022 | Blogs
Blockchain. Does it protect personal privacy? Is it a tool that can evade the law? How should we thi...

April 19, 2022 | Blogs
On March 31, 2022, the United States District Court for the Southern District of New York dismissed ...

March 31, 2022 | Blogs
Japan’s Act on the Protection of Personal Information (APPI) becomes effective on April 1, 2022. T...
March 25, 2022 | Blogs
The Department of Labor’s Employee Benefits Security Administration (DOL) issued Compliance Assist...
In the News:
Connected Vehicles & Automatic Decision-MakingPublication: Bloomberg Law
Publish Date: March 24, 2022

March 21, 2022 | Blogs
The Life of an Outsourced DPO The data protection laws of the European Union require many European a...

March 18, 2022 | Blogs
In recent years, online crowdfunding platforms such as Kickstarter, Indiegogo, and GoFundMe have eme...

March 11, 2022 | Publications
The Utah legislature recently passed the Utah Consumer Privacy Act (UCPA). UCPA is a comprehensive p...

March 9, 2022 | Blogs
President Biden issued an Executive Order (the “Order”) earlier outlining the administration’s...
March 1, 2022 | Blogs
The increased popularity of non-fungible tokens (NFTs) has potential to inspire new methods of creat...

February 17, 2022 | Blogs
Hacking – it gets a bad rap. For good reason. It’s associated with bad actors who infiltrate an ...

February 11, 2022 | Blogs
India is about to enact a far-reaching Data Privacy Law. Expected to be passed by April 2022 and in ...

January 28, 2022 | Blogs
Does a Privacy Apocalypse Draw Near? Quantum computing – some view its emergence as heralding the ...

January 28, 2022 | Blogs
Data Privacy Detective Podcast · Top 5 Tracks – Data Privacy Day 2022 Top 5 Tracks ...

January 24, 2022 | Blogs
Backup – what does it have to do with protecting data privacy? And how does a backup service work?...

January 18, 2022 | Blogs
Taiwan occupies a unique geopolitical position – with a substantial population and robust economy,...

January 5, 2022 | Blogs
Turkey is the first 2022 stop on our global tour about data localization. What is Turkey’s approac...

December 27, 2021 | Blogs
The Data Privacy Detectives turns his data localization spotlight on the island nation of Singapore....

December 6, 2021 | Blogs
Our prior podcast episodes detailed how China, Russia, and to a lesser extent India have created bar...

November 9, 2021 | Blogs
We turn to Russia in our data localization series. Russia’s 2015 personal data protection law requ...

November 2, 2021 | Blogs
In this second podcast episode about data localization, we spotlight India. Since 1993 the world’s...

October 21, 2021 | Blogs
The internet and the worldwide web – the words envision a global communications system that transc...

September 30, 2021 | Blogs
Home is our private place. But in the digital age, how private are our homes? And what can we do to ...

September 1, 2021 | Blogs
Kentucky is perhaps the first state to adopt a comprehensive anti-doxing statute that creates a civi...

August 30, 2021 | Blogs
Mike Potter’s cat bounced on his keyboard years ago. His hard drive cratered, and he lost his data...

August 5, 2021 | Publications
Driven by the pandemic, many brick-and-mortar businesses have rapidly undergone a digital transforma...

August 2, 2021 | Blogs
The state of Wyoming made headlines when its legislature approved a first-of-its-kind bill[1] that g...

July 28, 2021 | Blogs
Ransomware. It’s in the headlines. It’s digital organized crime across borders. When an organiza...

July 20, 2021 | Blogs
This article was originally published on July 19, 2021 in Westlaw Today, an imprint of Thomson Reut...

July 20, 2021 | Publications
Driven by the pandemic, many brick and mortar businesses have rapidly undergone a digital transforma...

July 8, 2021 | Blogs
Ransomware attacks, data breaches, digital theft – on the rise. Who are the cyber-criminals? Can t...

July 1, 2021 | Blogs
On June 28, 2021, the Europe Union granted two adequacy decisions to the United Kingdom for personal...

June 2, 2021 | Publications
Industry analysts and business consultants have agreed for some time that connected mobility is the ...

May 14, 2021 | Blogs
In order to keep up with a changing world, each company must periodically assess how technological c...

May 10, 2021 | Blogs
This is a true story of a phone scam of May 2021. The Data Privacy Detective got a call on the home ...

May 3, 2021 | Blogs
This podcast episode explores ransomware from preventive, legal, and communications angles. While th...
April 22, 2021 | Publications
There is a growing trend in support of “right to repair” laws requiring manufacturers to make th...
April 9, 2021 | Blogs
On April 5, the U.S. Supreme Court found that Google’s copying of Oracle code was fair use, puttin...

April 2, 2021 | Blogs
Janus was the Roman god of doors, gates, and transitions. He needed two faces to look in both direct...

April 1, 2021 | Blogs
Your vendor wants to use A Blockchain “Smart Contract” for the transaction. Now what? At a glanc...

March 29, 2021 | Blogs
Kentucky has long been considered a national leader in the manufacturing industry given its low cost...

March 25, 2021 | Blogs
Facial recognition. It’s a hot topic. Targeting, misidentification, and doxing – the dangers...

March 22, 2021 | Publications
The California Consumer Privacy Act (CCPA) came into effect on January 1, 2020, to regulate the data...

March 18, 2021 | Blogs
Distributed ledger technologies (DLTs) are becoming more prominent with applications across supply c...

March 15, 2021 | Publications
The automotive industry continues to evolve, especially in how intellectual property is developed an...

February 17, 2021 | Blogs
Challenges from Europe and America On February 16, 2021 TikTok was sued in Europe for abusing consum...

February 11, 2021 | Publications
Blockchain technology, best known as the distributed ledger platform that powers Bitcoin and other c...

January 28, 2021 | Blogs
Data theft set new records in 2020. The major causes are not failures of equipment, software, or ser...

January 12, 2021 | Blogs
Data theft set new records in 2020. The major causes are not failures of equipment, software, or ser...

January 8, 2021 | Publications
More than 5,300 companies in the United States used the EU-US Privacy Shield Framework for the tra...

January 5, 2021 | Blogs
As businesses move into 2021, what insurance can they have to limit cyber risk? What does cyber insu...

December 22, 2020 | Blogs
Taiwan is one of the “Four Asian Tiger” economies. Its companies hold 66% of the world’s semic...

December 21, 2020 | Blogs
How a community can responsibly gather, process and use personal information to meet its needs and m...

December 4, 2020 | Blogs
Respecting individual privacy while achieving reliable databases. We all value privacy – at least ...

November 9, 2020 | Blogs
With the passing of Proposition 24 in California, privacy rights are being amended again to close wh...

November 5, 2020 | Blogs
Ransomware – a sinister type of cyberattack that installs malware onto a computer system. Once...

October 26, 2020 | Blogs
Science and knowledge advance through information gathered, organized, and analyzed. It is only thro...

October 5, 2020 | Blogs
The current COVID-19 crisis has increased the importance of online services that provide access to h...

October 1, 2020 | Blogs
The Impact on Privacy From a Digital Healthcare Initiative COVID-19 has changed the world in dramati...

September 25, 2020 | Blogs
Brazil’s General Personal Data Protection Law or “LGPD” entered into force on September 18, 20...

September 1, 2020 | Blogs
Robo-calls, phishing, identity theft, ads we didn’t ask for – and worse. How does this happen? H...

August 20, 2020 | Blogs
A July 2020 Indian Government Report calls for regulation of Non-Personal Data. Most data privacy la...

August 7, 2020 | Blogs
Cloud computing offers a business the prospect of efficiency and savings by improving data storage c...

July 31, 2020 | Blogs
On June 30, 2020 China enacted a National Security Law applicable in Hong Kong. The UK and USA gover...

July 27, 2020 | Blogs
Be Smart The pandemic has forced many more employees to work from home. While working remotel...

July 24, 2020 | Blogs
On July 22, 2020, the Office of the Comptroller of the Currency (“OCC”) released Interpretative ...

July 24, 2020 | Blogs
Effective July 15, 2020, Kentucky statutorily empowered its first “Blockchain Technology Working G...

July 17, 2020 | Blogs
More than 5,300 companies in the United States using the EU-US Privacy Shield Framework for the tran...

July 6, 2020 | Blogs
Colombia made personal privacy a fundamental right in its 1991 Constitution. A 2008 law protected pe...

June 26, 2020 | Blogs
Every year approximately $600 billion, or 1% of the global gross domestic product, is lost through c...

June 4, 2020 | Blogs
On June 1, Attorney General Becerra submitted final proposed regulations to the California Consumer ...

June 3, 2020 | Blogs
A federal district court in In re: Capital One Customer Data Security Breach Litigation recently ...

May 21, 2020 | Blogs
Often seen as a region with a common language and similar cultural traditions, Latin America is, in ...

May 6, 2020 | Coronavirus Response Team
In this unfamiliar time, innovative solutions are being rapidly developed in the technology industry...

May 4, 2020 | Blogs
Newly published federal rules will now give more power to consumers in controlling their personal he...

April 24, 2020 | Coronavirus Response Team
There are several ways startups raise funding – one of the most prevalent is a convertible note. A...

April 3, 2020 | Publications
You may have seen in the news that consumer information privacy laws have become a hot topic around ...

March 26, 2020 | Coronavirus Response Team
Embracing both patents and patented technology may advance the fight against COVID-19. In Italy, the...

March 23, 2020 | Publications
Recalling the Wild West’s gold rush of the 1800s, today’s data is gold, and it has busin...

March 23, 2020 | Blogs
As the coronavirus continues to quickly spread across the United States, employers are following CD...

March 12, 2020 | Publications
On March 11, California Attorney General Becerra, through the California Department of Justice, rele...

March 10, 2020 | Blogs
Customedia v. Dish is a simple looking case. The patentee asserted claims for a computer implement...

March 9, 2020 | Blogs
Bankers in the fintech space are familiar with the FFIEC’s Guidance recommending multi-factor auth...

February 12, 2020 | Publications
Barely a month into the new year and nine states have already introduced their own version of compre...

February 10, 2020 | Blogs
On Friday, February 7, California Attorney General Becerra released proposed modifications to the dr...

January 31, 2020 | Blogs
The United Kingdom (UK) has formally withdrawn from the European Union (EU) effective January 31, 20...

January 7, 2020 | Blogs
Governmental officials and cyber security experts currently anticipate that Iran’s responses to re...

January 6, 2020 | Publications
Businesses have more than the California Consumer Privacy Act (CCPA) to worry about in 2020 when it ...

December 23, 2019 | Blogs
California’s Consumer Privacy Act goes live on January 1, 2020. It forces businesses beyond...

November 18, 2019 | Blogs
Medical data are considered particularly sensitive personal information. Laws and regulations in...

September 17, 2019 | Blogs
Friday, Sept. 13 was the last day for bills amending the California Consumer Privacy Act (CCPA) and ...

August 16, 2019 | Blogs
A federal court in California handed Delta Air Lines a win this year by dismissing a putative class ...

August 15, 2019 | Blogs
States across the U.S. are rapidly passing new consumer privacy laws. This is the second in an ongoi...

July 10, 2019 | Blogs
Substantive Expertise versus A New Perspective and Freedom from the Past Counsel are regularly and a...

July 8, 2019 | Blogs
As the scale of solar energy projects grows, the incorporation of advanced direct current (DC) monit...

July 5, 2019 | Blogs
Background Blockchain technology’s potential for disintermediation in the financial sphere has evo...
June 13, 2019 | Blogs
In Dept. of Labor v. McConnell, the Georgia Supreme Court affirmed that an individual could not pur...

May 14, 2019 | Blogs
As we roll into 2019’s peak travel season, automakers are hitting the gas on developing the necess...

May 13, 2019 | Blogs
The May 2-3, 2019 International Association of Privacy Professionals (IAPP) Conference featured lead...

April 30, 2019 | Blogs
Fifty years ago, auto manufacturing plants were filled with thousands of people on large assembly li...

April 30, 2019 | Blogs
Picture frontline employees – like those at a motel’s front desk. In enter ICE agents with gold ...

April 15, 2019 | Blogs
The practical effect of the GDPR in connection with domain name enforcement can leave (and should le...

April 11, 2019 | Blogs
The California Consumer Privacy Act (CCPA) goes into effect on January 1, 2020. Before then, covered...

March 7, 2019 | Blogs
Businesses that violate the CCPA can face civil penalties in actions brought by the California Attor...

March 4, 2019 | Blogs
The CCPA can apply to businesses located outside California that collect or sell personal informatio...

March 4, 2019 | Blogs
Data incidents arise regularly for businesses. The perpetrators range from sophisticated scoundrels ...

February 19, 2019 | Blogs
On December 28, 2018, the former Michigan Governor, Rick Snyder, signed into law House Bill 6941 (th...

January 4, 2019 | Blogs
The European Commission issued its second review of how the EU PrivacyShield is working in late Dece...

November 6, 2018 | Blogs
“The internet is growing less free around the world, and democracy itself is withering under its i...

October 1, 2018 | Blogs
In recent years, cryptocurrencies, such as Bitcoin, Ripple, Ethereum, and Kin, have brought a flur...

September 21, 2018 | Blogs
TL;DR: Drone services companies need to get their drone operators to sign intellectual property as...

September 5, 2018 | Blogs
Have you heard about the California Consumer Privacy Act (CCPA) that recently passed and goes into...

August 9, 2018 | Blogs
On Friday, August 3, Governor Kasich signed Ohio Senate Bill 220, which acknowledges for the first t...

July 30, 2018 | Blogs
The European Union’s General Data Protection Regulation (GDPR), effective as of May 25, 2018, ...

July 26, 2018 | Blogs
When Congress enacted the Communications Decency Act of 1996, the internet was an infant. Prevaili...

July 9, 2018 | Blogs
“California passes strictest online privacy law in the country,” trumpeted CNN Tech on...

June 18, 2018 | Blogs
Businesses not located in the European Union have tried to understand whether the General Data Pro...

June 1, 2018 | Blogs
It’s June 1, 2018, one week after the General Data Protection Regulation of the European Union bec...

May 16, 2018 | Blogs
GDPR, the European Union’s effort to protect personal data, has dominated the efforts of businesse...

April 26, 2018 | Blogs
In our prior podcast, the Data Privacy Detective explored how non-EU businesses can determine if t...

April 19, 2018 | Blogs
In this and the next podcast, the Data Privacy Detective turns a magnifying glass to how businesse...

April 18, 2018 | Blogs
On April 17, 2018, New York Attorney General Eric T. Schneiderman (the “NY AG”) launched...

April 17, 2018 | Blogs
The European Union’s General Data Protection Regulation, the GDPR, becomes directly applicab...

April 10, 2018 | Blogs
The EU’s GDPR – the General Data Protection Regulation – becomes law on May 25, ...

April 9, 2018 | Blogs
In this fourth podcast about the General Data Protection Regulation that becomes law in the Europe...

April 2, 2018 | Blogs
Businesses collect, use and store personal data. It’s unavoidable. An email address, phone n...

March 29, 2018 | Blogs
The General Data Protection Regulation – the GDPR - becomes law throughout the European Unio...

March 26, 2018 | Blogs
On May 25, 2018 the European Union’s General Data Protection Regulation becomes law – ...

January 10, 2018 | Blogs
SEC issues cease-and-desist order two days into the Munchee ICO, a sign the Commission is inchi...

December 11, 2017 | Blogs
This is the second article in a series on the legal issues surrounding artificial intelligence (AI...

November 21, 2017 | Blogs
Full webinar about legal issues surrounding AI. This is the first article in a series on the l...

August 25, 2017 | Blogs
In this podcast, the Data Privacy Detective talks about tech support scams with Michael Severini, ...

August 9, 2017 | Blogs
IoT – the Internet of Things – is the interconnection of physical objects and data. Sm...

August 3, 2017 | Blogs
Phishing is an effort by cybercriminals to use bait in the guise of a familiar email address to ho...

July 28, 2017 | Blogs
On July 25, 2017, the FBI issued a TLP:AMBER alert on its Cyber Watch system about an elaborate cy...

May 4, 2017 | Blogs
The practice of law is going to look very different 15 years from now. The most routine legal work...

December 1, 2016 | Blogs
The Data Privacy Detective met with Ken Morris, lawyer, technologist and founder of KnectIQ, to di...

November 28, 2016 | Blogs
In late October 2016, the Data Privacy Detective met with Joe Tomain, a visiting lecturer at India...

November 22, 2016 | Blogs
An Excerpt from when the Data Privacy Detective sat down with Julia Montgomery to discuss data pro...

November 4, 2016 | Blogs
Initial coin offerings (ICOs) are garnering substantial attention as investors hope their digital ...

October 17, 2016 | Blogs
I attend conferences of our international law firm network MULTILAW. It’s a gathering of law...

October 13, 2016 | Blogs
It seems like everyone is discussing “blockchain,” but few have taken the time to real...

October 10, 2016 | Blogs
The word “computer” was once an occupational classification. Computers were workers wh...

October 9, 2016 | Blogs
I spoke about America’s approach to data privacy at a recent Conference at the European Cour...

October 7, 2016 | Blogs
Privacy is dead, get over it. This is what a blockchain entrepreneur told a Conference at the Euro...




